New in SpyWeek: Threats
Netanyahu joins Russia, China & Iran as challenges to U.S. security, while Open Source intel presents opportunities. But "mediocrity' still hobbles CIA management.
Welcome to SpyWeek, our weekly newsletter, where we look at news from the intersection of intelligence, foreign policy, and military operations.
Worldwide Threats:
The Office of the Director of National Intelligence released its Annual Threat Assessment on Monday, offering the collective judgment of the U.S. intelligence community on what it calls an “increasingly fragile world order.”

The IC’s assessment that Israeli Prime Minister Benjamin Netanyahu's days in office may be numbered dominated the headlines. “Netanyahu’s viability as a leader as well as his governing coalition of far-right and ultra-orthodox parties that pursued hardline policies on Palestinian and security issues may be in jeopardy,” the report states. “A different, more moderate government is a possibility.” Senate Majority Leader Chuck Schumer, D-N.Y., the highest-ranking Jewish elected official in the United States, called for new leadership in Israel Thursday in a speech on the Senate floor.
Netanyahu has promised “total victory” over Hamas and declared that the leaders of the U.S.-designated terror group that killed 1,200 Israelis in a surprise attack on Oct. 7 are “all dead men.” But the U.S. intelligence community predicts that Israel will “probably” face lingering armed resistance from Hamas “for years to come.” The Israeli military “will struggle” to wipe out the group’s underground network of tunnels, “which allows insurgents to hide, regain strength, and surprise Israeli forces.” The risk of escalation of the conflict remains high.
Meanwhile, the Oct. 7 attack has reinvigorated al-Qaeda and ISIS, which have directed their supporters to carry out attacks against U.S. and Israeli interests, according to the threat assessment. “The crisis has galvanized violence by a range of actors around the world. And while it is too early to tell, it is likely that the Gaza conflict will have a generational impact on terrorism,” Avril Haines, the director of national intelligence, told the Senate Monday.
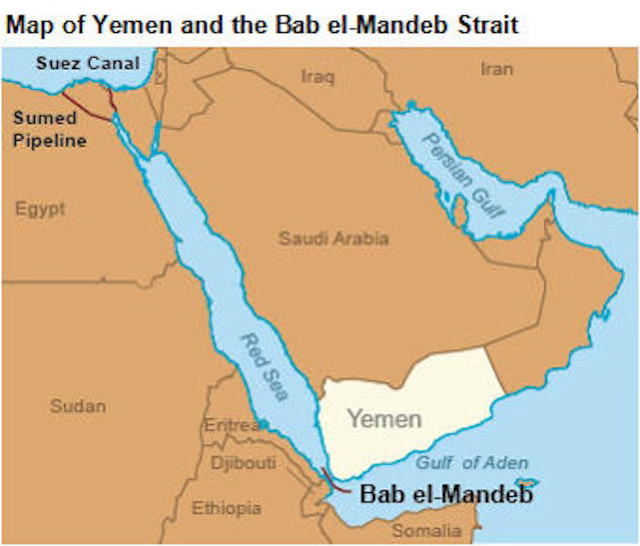
Iran’s role (or lack thereof) in the attack also got some attention. The intelligence community believes that Iranian leaders “did not orchestrate nor had foreknowledge of” the surprise attack by Hamas. After the attacks, however, Tehran was able to use its network of proxies across the Middle East to orchestrate anti-Israel and anti-U.S. attacks from Lebanon to the Bab el-Mandeb Strait, which lies between Yemen and Ethiopia.
Meanwhile, China is growing its nuclear stockpile, space weapons, and cyber capabilities, but a sentence about social media giant TikTok in the threat assessment drew attention on Capitol Hill: “TikTok accounts run by a [People’s Republic of China] propaganda arm reportedly targeted candidates from both political parties during the U.S. midterm election cycle in 2022,” it said.
TikTok wasn’t mentioned in last year’s threat assessment, and its inclusion in this year’s report spurred House members Wednesday to approve legislation intended to force China's ByteDance to sell TikTok or be banned from the United States. Haines told the House Tuesday, “We cannot rule out that the CCP would use” TikTok to influence the 2024 U.S. elections.
The Paradox of Intelligence Failures: As every boxer knows, the punch you didn’t see coming is the one that knocks you out.
Hamas wasn’t even mentioned in last year’s Annual Threat Assessment. Eight months later, the group’s Oct. 7 surprise attack killed 1,200 Israelis, started a war, inflamed the Middle East, and upended U.S. politics and internal relations. Hamas’ attack was the punch no one saw coming.
The CIA’s core responsibility is to prevent “strategic surprise,” the agency’s new deputy director for operations, Tom Sylvester, said recently on “The Langley Files,” a CIA podcast. The public knows strategic surprise by another name: intelligence failures.